Security & sovereignty, by design
Maleus is built for high-constraint environments: large enterprises, the public sector, government. Your IT stays your IT: your data, your code, your infrastructure.
Three ways to run Maleus
Choose the model that fits your risk posture. Each one is a different answer to a simple question: where does the data live, and who operates the infrastructure?
SaaS: Maleus cloud
Hosted by Maleus on AWS in the Paris region. The fastest way to get started, for organizations without a strict data-localization constraint.
- Data: AWS, Paris region
- Operated by: Maleus
Private cloud: bring your own cloud
Deployed into your own cloud account. You keep control of your infrastructure, and the LLM gateway can run through Bedrock or Azure.
- Data: your cloud account
- Operated by: you, with Maleus
On-premise
Deployed inside your own datacenter, including Kubernetes environments. For the strictest sovereign and government contexts.
- Data: never leaves your IT
- Operated by: you
Each model has a different cost profile, see how deployment affects pricing.
Your data stays where it belongs
Data residency
Data stays in the region or country you choose. On-premise, it never leaves your information system at all.
Isolation
A dedicated tenant per customer, with separate staging and production accounts: a dedicated account for each customer application.
No mixing
One customer's data is never used for another. No model is ever trained on your data. In bring-your-own-cloud mode, the LLM gateway can be your own: Bedrock or Azure.
Dedicated tenants, no path between them
No gateway, no shared store, no cross-tenant access.
Four pillars, built in from the start
Security is not a layer added at the end. It is a property of how the factory is built: isolation, a hardened core, and tight control over what runs and what ships.
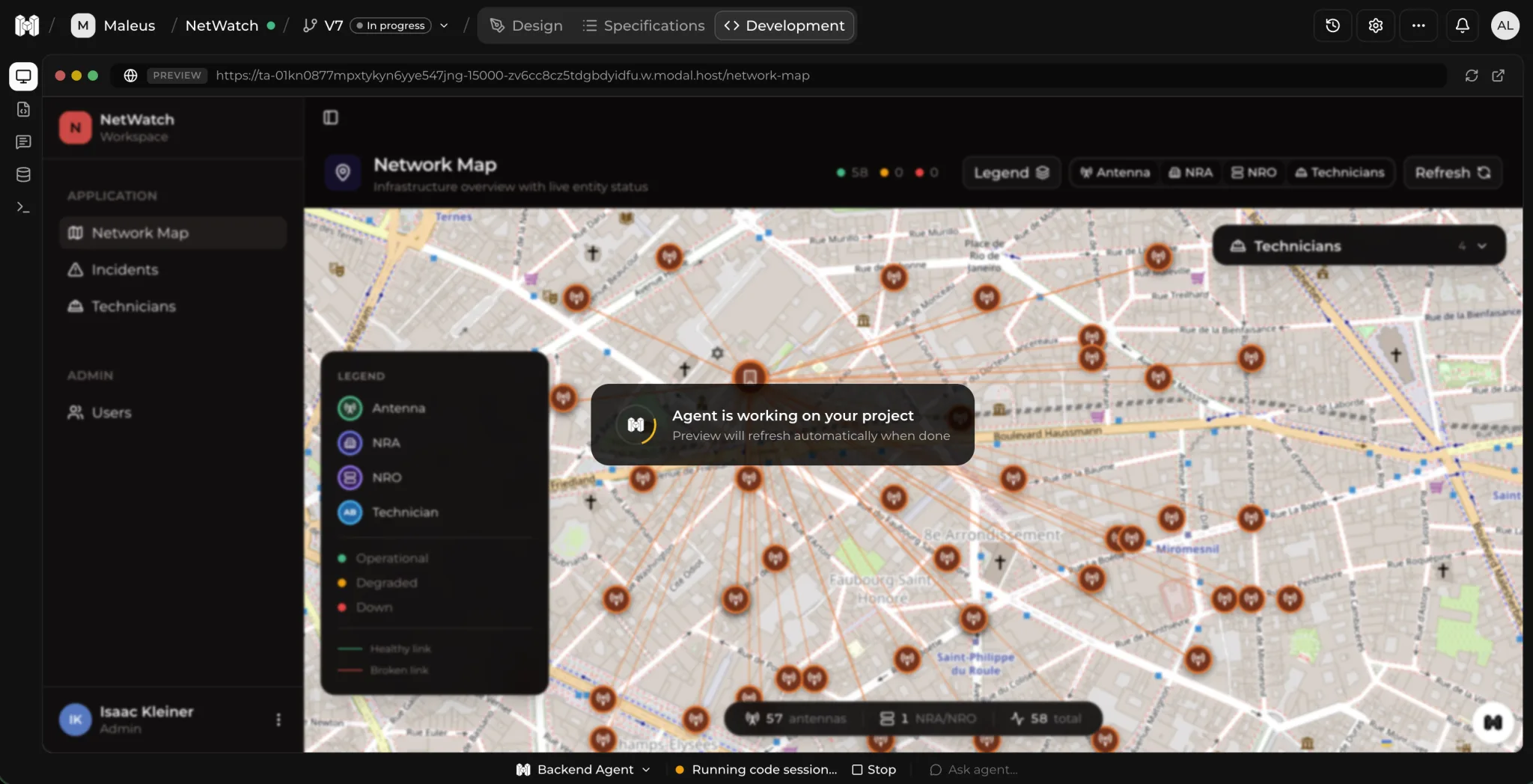
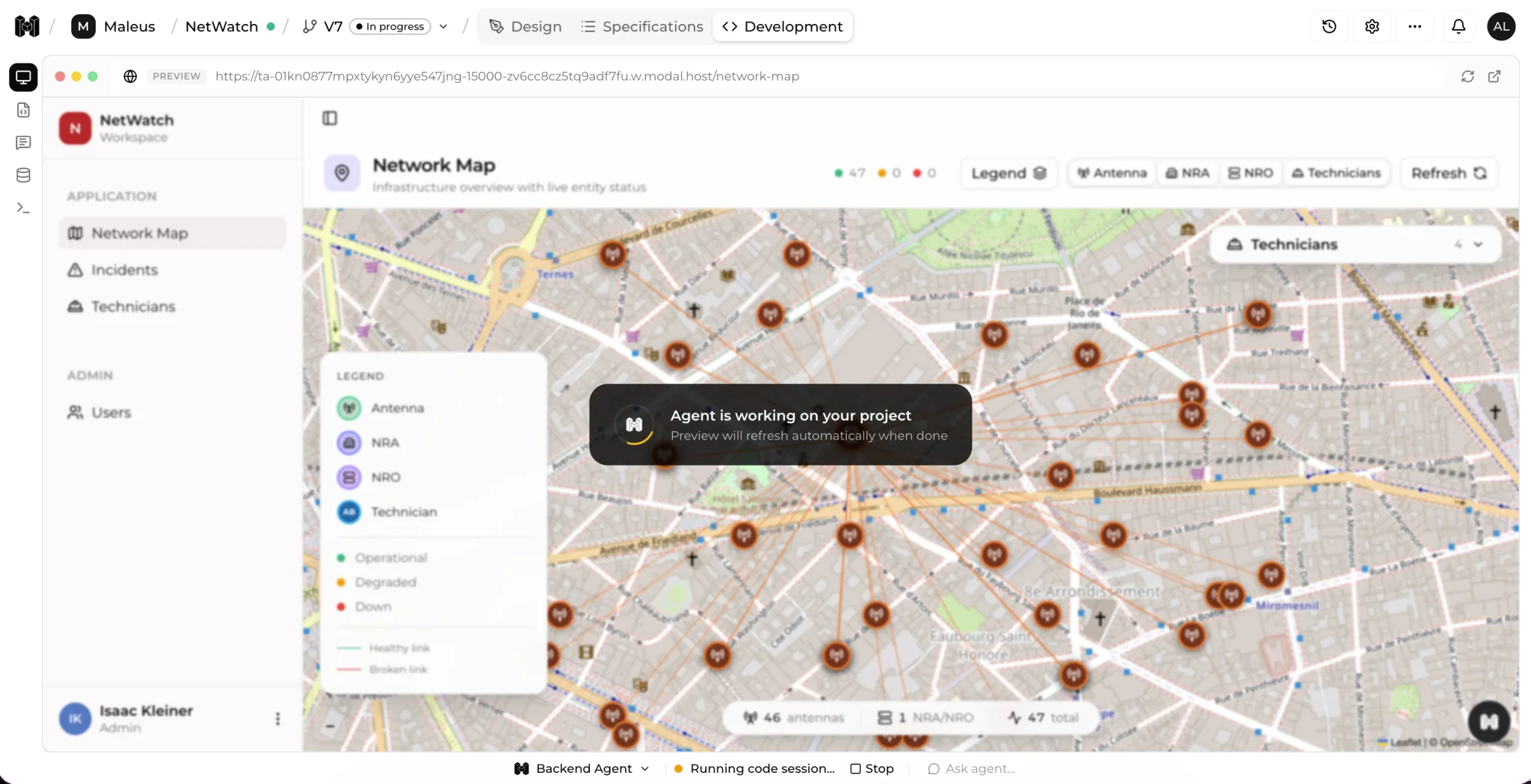
Isolated environments
Each agent works in an isolated, ephemeral environment: a sandbox created on demand and destroyed afterwards. Isolation runs at the kernel level, with an allowlist of permitted binaries.
Hardened core, not generated
Authentication, encryption, permissions and tenant isolation rest on a pre-built, hardened framework. The AI only generates business logic, never the critical security building blocks.
Supply-chain protection
Attacks targeting developer workstations are a major industry risk. Secrets are isolated per process, with no cross-process access.
Dependency control
Version freezing and controlled dependency management keep vulnerable packages from being introduced silently into your software.
The controls your RFP asks for
A direct answer to the checklist: connect Maleus to the identity and access stack you already run.
SSO: SAML / OIDC
Connects to your existing enterprise directory.
RBAC
Differentiated roles for read, edit and administration.
MFA
Multi-factor authentication on every account.
Secrets management
A secrets vault, with secrets isolated per process.
Where we stand, without sugar-coating
We are in a pilot phase and building our compliance methodically. Here is the honest state of each framework: no certification is shown as obtained before it is.
Controls are being implemented and the observation period is underway. Audit planned: request our security documentation for the current timeline.
Our information security management system is being built against Annex A. Certification is in preparation.
Records of processing maintained, DPA available on request, and EU data hosting available. We process EU customer data accordingly.
Last updated: May 2026
Request our security documentation & reportsA secure tool is not the same as secure code
Most competing tools claim ISO 27001, but they only certify their own tool, not the software it produces. Maleus secures the code delivered to you.
The software Maleus generates is itself production-grade and hardened. When a vulnerability is found, we can distribute a fix to applications already generated, for example, correcting a password-hashing flaw across every app we have delivered.
What others certify
Delivered applications are out of scope.
What Maleus secures
Every delivered application, patched.
Automatic security analysis of the code produced: vulnerability scanning and dependency auditing.
Code quality measured continuously, so security and maintainability are verifiable.
Everything is traced
Full audit trail
Every action is recorded: a complete, traceable log of agent sessions.
Correlated logs
Interactions, API requests and backend logs, tied together for investigation.
SIEM integration
Forward events to your existing SIEM and keep security monitoring in one place.
Human sign-off
Mandatory approval before any infrastructure deployment. No blind deployments. Incidents are categorized and escalated.
The code is 100% yours. No vendor lock-in.
The software Maleus generates belongs entirely to you. It runs on its own, with no operational dependency on the platform. You keep your code and can take it back over whenever you want.
- Standard code, open-source technologies
- Applications run independently of the platform
- Connect your GitHub or GitLab and take the code anytime
Want to see how the software is built? Explore the platform.
A security question? Let's talk it through.
Our technical team answers security questionnaires and documentation requests directly, no sales detour required.